Compliance | Don’t get taken by surprise.
By David Pretorius • January 31, 2024

Lets reset expectations!
Over the last 2-3 years, we have been working with our contracted clients on their compliance journey around Cyber Security, Essential 8 or ISO27001.
The first step, is usually the hardest and most commonly, it involves getting EVERYBODY ( board, owners, exec’s, staff and IT ) to all agree that things ARE NOT 100% secure and compliant and that we need to start somewhere.
It is much more important to be honest with what % compliance a company is currently at and having a plan to address the gaps VS pig headedness.
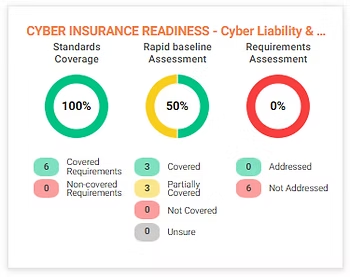
The below image is a typical organization’s dashboard approximately 3 months into a monthly compliance engagement, in that, the board | exec’s are aware that;
- All
requirements
have been articulated, reviewed and selected from a relevant
standard.
- All
requirements
have had possible
controls
identified that will meet the
requirements.
- Of those
controls, there are no “unsure“, like there would be at the beginning of the process.
- The organisation is;
- 50% through the process BUT, depending on budget, timing and other business pressures, they might be 12 - 18 months away from 100%
- ready and expecting that Insurance companies will add extra requirements each year.
- aware that the Australian Government will continue to lift the awareness of cyber awareness (
Small business | Cyber.gov.au
)
Summary
Any small to medium business can start the journey, and the journey simply takes scheduled time and diligence BUT it will be a waste of time if the board or owners won’t take that HONEST first step of assessment.
GREEN
is the goal, but it starts with mostly
RED.
A typical dashboard approximately 3 months into a compliance journey
Latest Posts